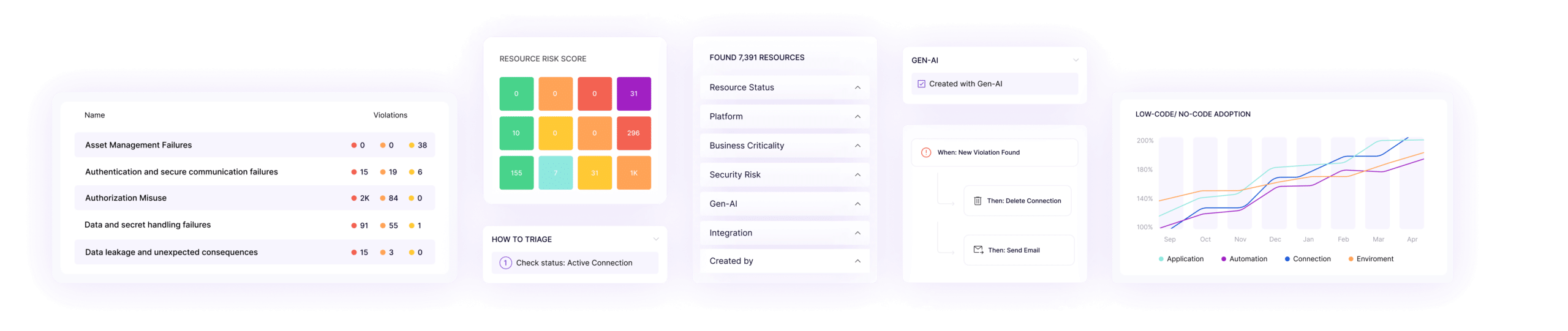
Citizen Development Application Protection Platform (CDAPP)
- Continuous scanning of AI, low-code, and no-code environments
- Assess risk and vulnerabilities for each individual application
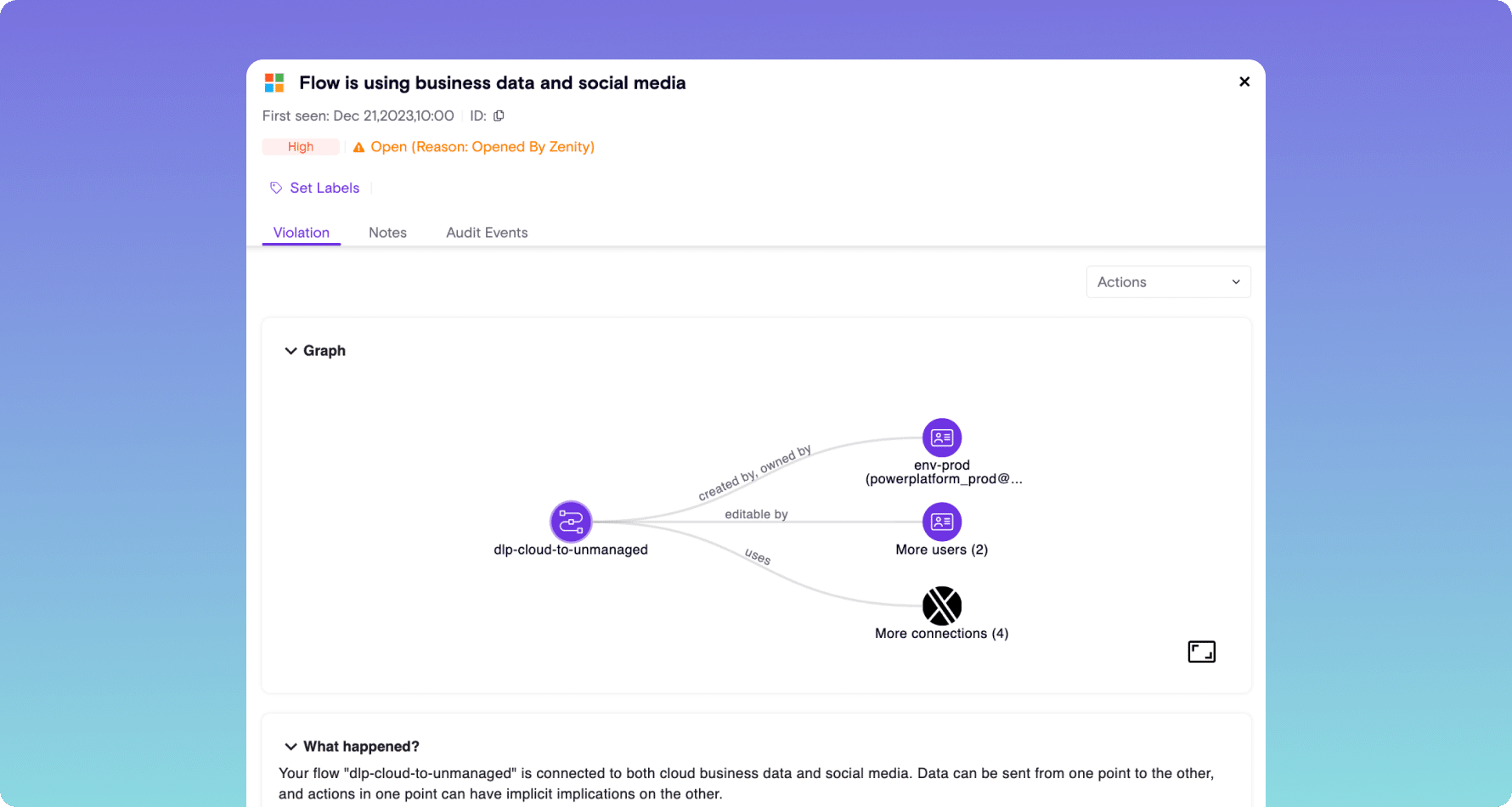
- Graph-based visibility and response
App Security Posture Management (ASPM)
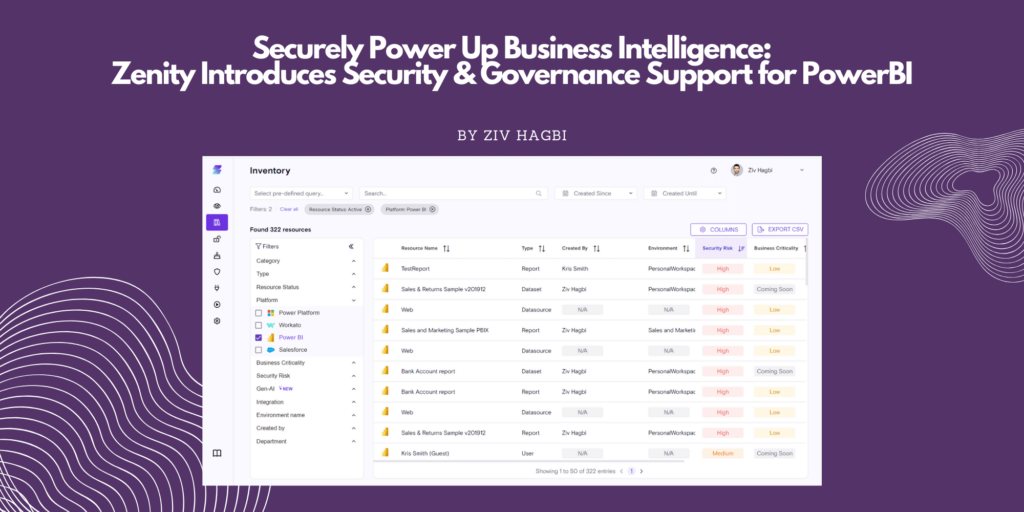
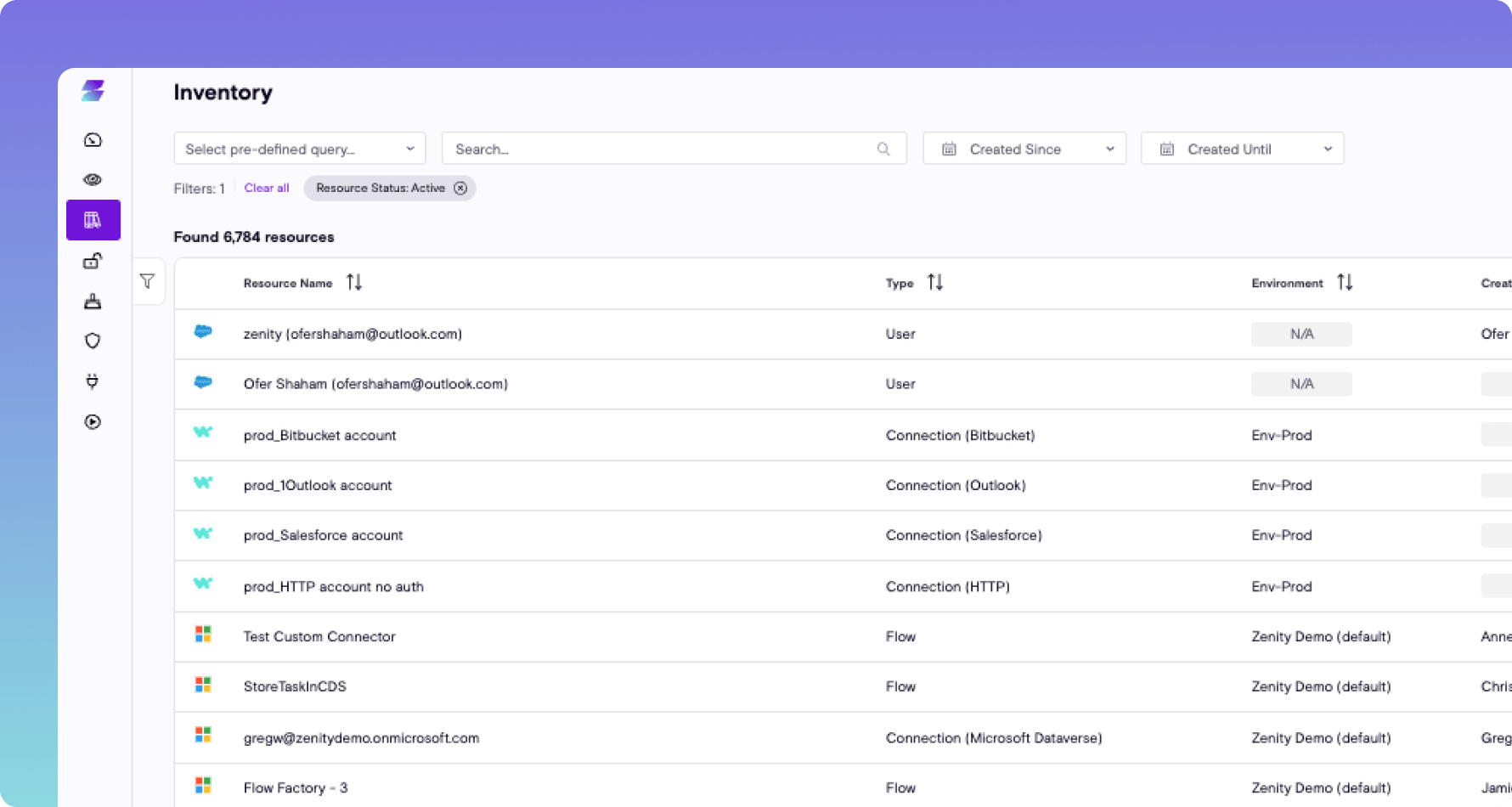
- Centralize visibility and inventory of all applications created across different platforms
- Implement least privilege to ensure apps are only shared and used by authorized users
- Identify apps that interact with sensitive data
- Implement guardrails for who can develop what and how within various low-code platforms
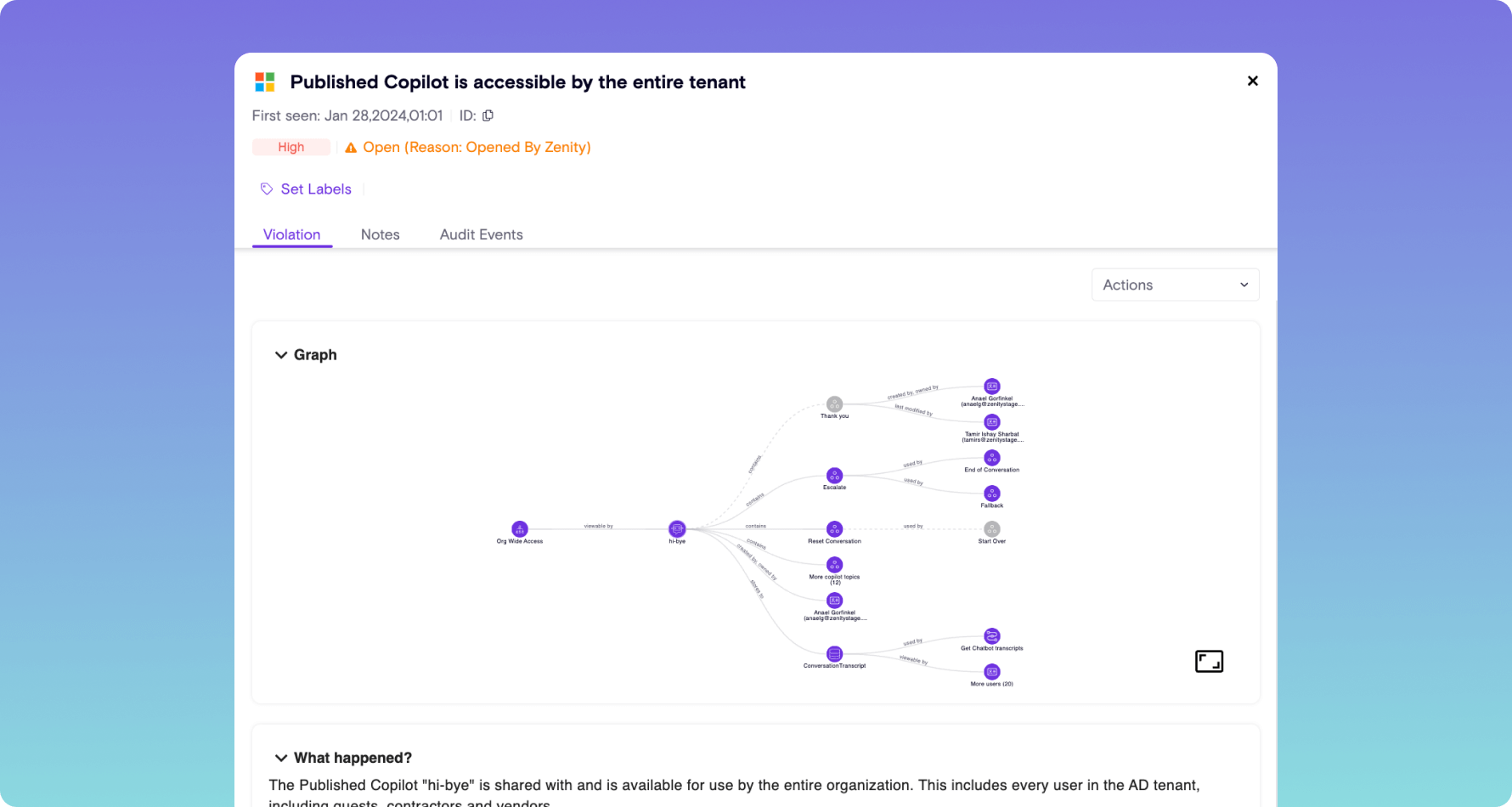
AI Security Posture Management (AISPM)
- Continuous scanning to identify bots and copilots that leverage Gen AI
- Implement least privilege to ensure that Copilots are only shared and used by authorized users
- Identify copilots and bots that interact with sensitive data
- Playbooks/policies to implement guardrails for who can develop what and how within various low-code platforms
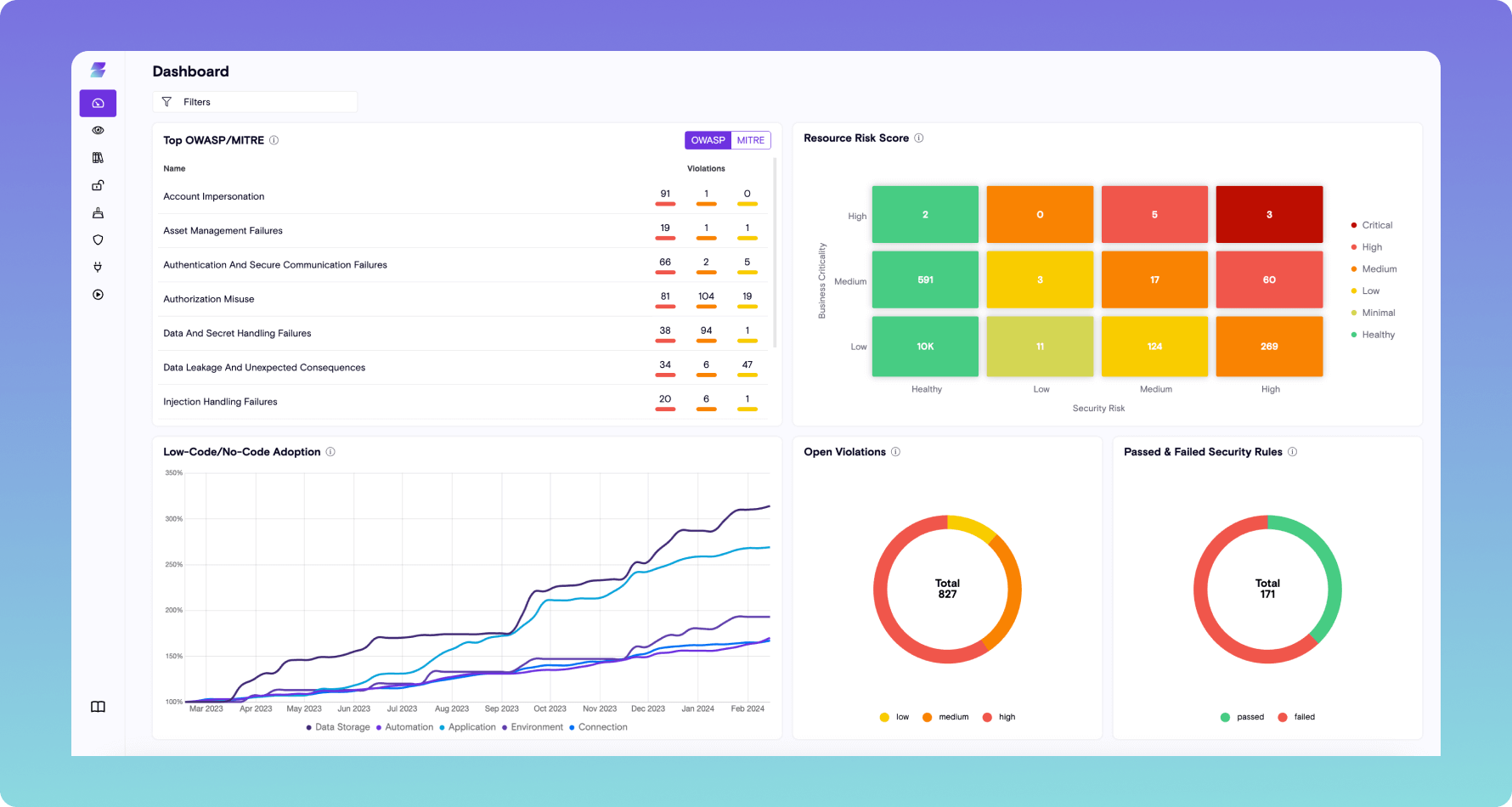
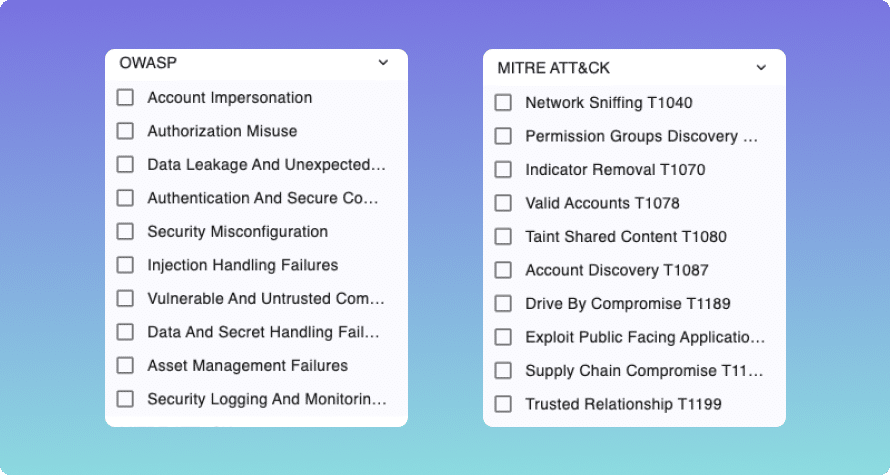
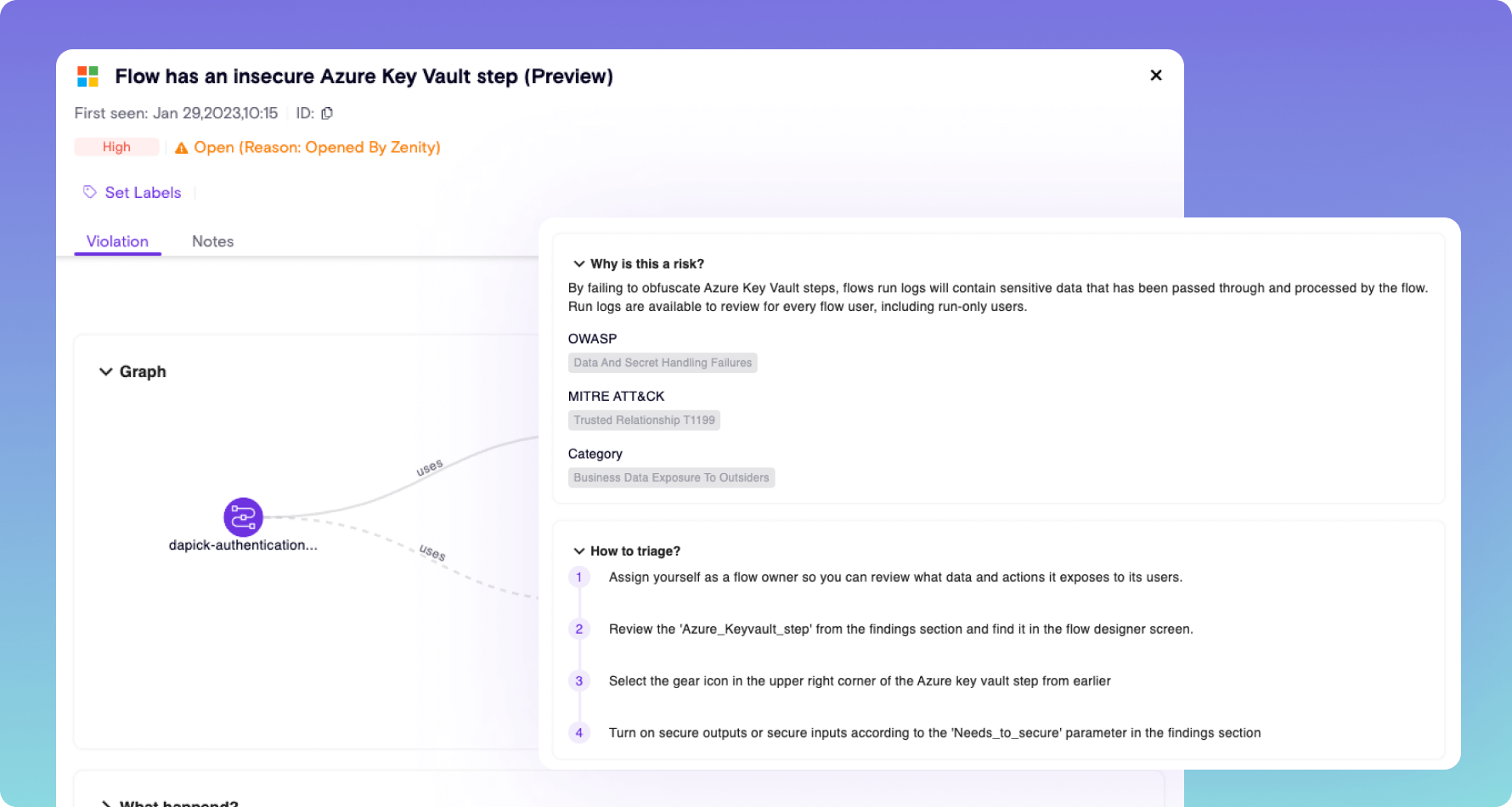
Vulnerability Management
- Scan each individual app, automation, and copilot for risk and map vulnerabilities to popular security frameworks
- Identify common vulnerabilities like User Impersonation, data leakage, credentials sharing, hard-coded secrets, and more
Secrets Scanning
- Identify hard-coded credentials baked into applications as they are built
- Automate response with playbooks and policies to prevent malicious or unauthorized use
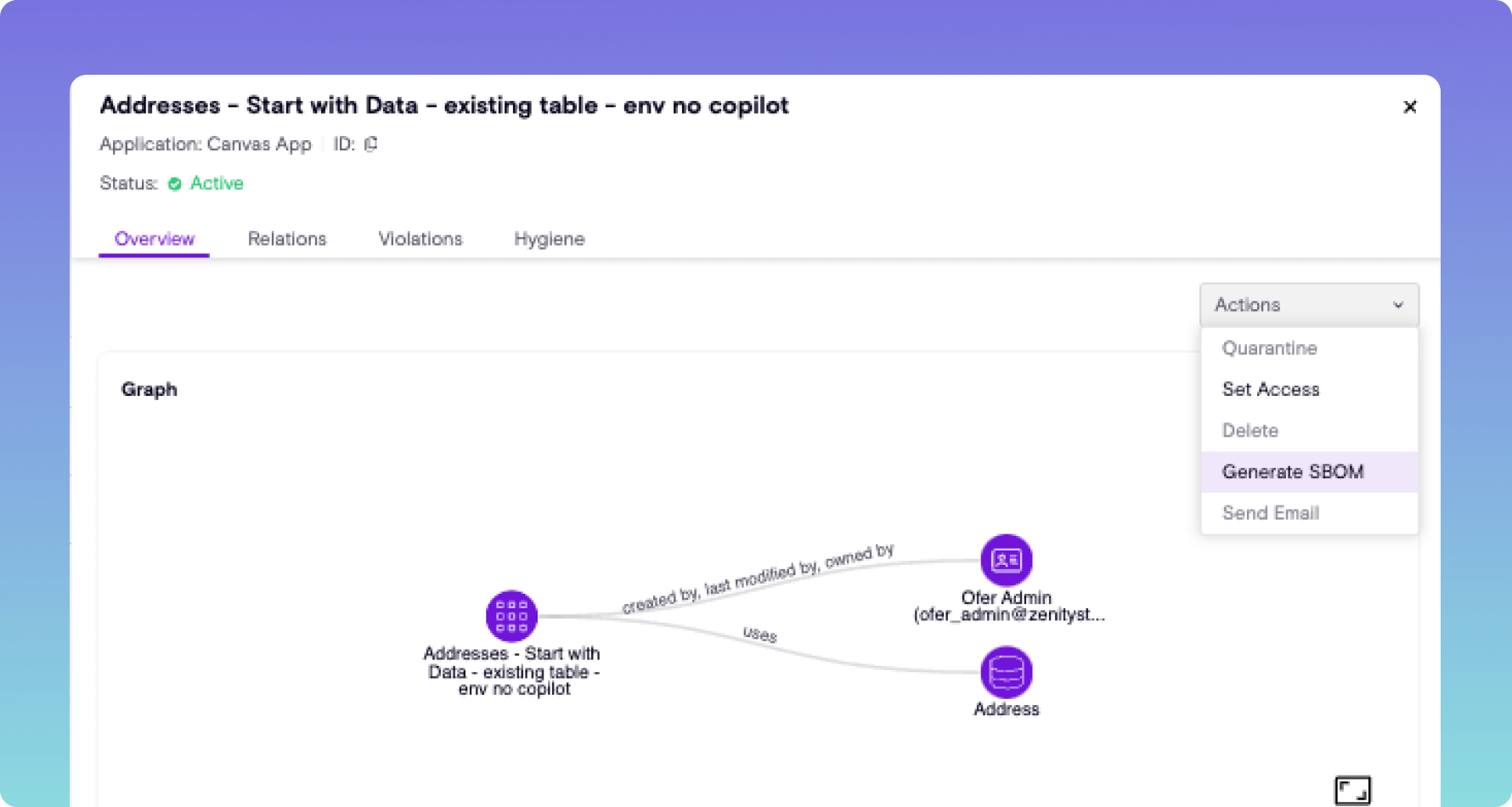
Software Composition Analysis
- Craft robust third-party dependency analysis and SBOM for professional and citizen developed applications and AI copilots
- Identify all third-party components that are used in each individual app, automation, and copilot
Data Security Posture Management (DSPM)
- Analyze all flows to establish what data is taken outside of the corporate environment into personal accounts, external users, etc
- Identify and classify data that each individual application, automation, and Copilot interacts with, and tagging information that is labeled as sensitive
- Implement guardrails to prevent apps, automations, and copilots from being built that leak data